Mission Statement
The mission of NCSC's Supply Chain and Cyber Directorate (SCD) is to enhance the nation's supply chain and cyber security, leveraging multidisciplinary counterintelligence and security expertise to inform, guide, and coordinate integrated risk decisions and responses with strategic partners.
PROTECTING CRITICAL SUPPLY CHAINS
A Guide to Securing Your Supply Chain Ecosystem
Building a Resilient Ecosystem
Protecting Critical Supply Chains: Risks From Adversarial Exposure

Protecting Critical Supply Chains: Cyber Threat Hunting
CHAMPION SUPPLY CHAIN
Take the General Services Administration (GSA) and Federal Acquisition Institute (FAI) training course to Fortify the Chain:
- FAC-093: "Introduction to Supply Chain Risk Management"
- Requires Defense Acquisition University (DAU) account or Department of Defense (DoD) Common Access Card (CAC)
Protecting Supply Chains for Critical Technologies
In October 2021, the National Counterintelligence and Security Center (NCSC) prioritized outreach efforts in five critical technology sector areas: Artificial Intelligence (AI), Bioeconomy, Autonomous Systems, Quantum, and Semiconductors.
These technologies present unique opportunities and challenges where the stakes are potentially greatest for U.S. economic and national security.
One of the unique challenges is managing the threats and risks to the very complex supply chains that support each one of these critical and emerging technologies.
For National Supply Chain Integrity Month in April 2022, NCSC focused on supply chain security issues unique to AI, specifically machine learning (ML) an AI subset; autonomous systems, specifically autonomous vehicles; and semiconductors
The awareness materials below highlight the unique supply chain issues associated with these critical technologies.
- Autonomous Automotive Vehicle Supply Chain Risk
- Information and Communications Technology and the Supply Chain Risk
- Managing Supply Chain Risk to Machine Learning
- Supply Chain Risks to Semiconductors
National Supply Chain Integrity Month
April 2024—#SCRM is the A.C.E.
Don't let threat actors have the upper hand.
Play an A.C.E.
- Acquisition Security
- Cyber Security
- Enterprise Security
- Press Release — April 2024 National Supply Chain Integrity Month
- Supply Chain Integrity Month Calendar
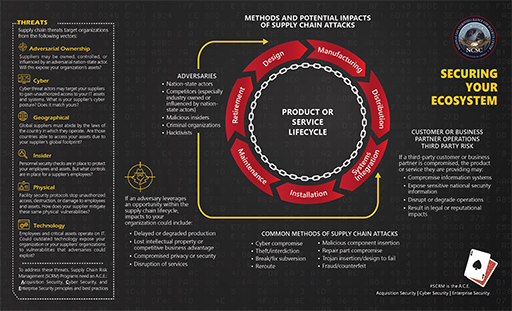
Securing Your Ecosystem: Methods and Potential Impacts of Supply Chain Attacks
April 2023 — Supply Chain Risk Management (SCRM) – The Recipe for Resilience
- Zero-Trust Architecture
- Software Supply Chain Attacks
- Critical Minerals Supply Chain Resilience
- 5G Network Slicing – C-SCRM Best Practices
- Ransomware Threats and Impacts to Industry
- Venture Capital and Supply Chain Vulnerabilities
April 2022 — Fortify the Chain
- April 2022 National Supply Chain Integrity Month press release
- April 2022 NSCIM calendar of events
- Agri-Food Supply Chain Spotlight
- Defense Industrial Base Supply Chain Spotlight
- Energy Supply Chain Spotlight
- ICT Supply Chain Spotlight
- Public Health Supply Chain Spotlight
- Transportation Supply Chain Spotlight
- Supply Chain Cyber Attacks
- Baker's Dozen - 13 Elements of an Effective SCRM Program
- Podcast: Securing U.S. Supply Chains - Addressing Our Vulnerabilities with Jeanette McMillian
April 2021 — A Call to Action
- Press Release: National Supply Chain Integrity Month – A Call to Action
- Software Supply Chain Attacks – 2021
- Supply Chain Risk Management: Best Practices in One Page – 2021
- Framework for Assessing Risks - 2021
- Sector-Specific Supply Chain Best Practices
Supply Chain Risk Management (SCRM) - Don't Be the Weakest Link!
- NCSC SCRM Best Practices
- Intelligence Community Logistics and SCRM
- NCSC Supply Chain Risk Management video
- 2018 Foreign Economic Espionage in Cyberspace report
- NCSC Federal Partner Newsletter: National Supply Chain Integrity Month
- MITRE report: Deliver Uncompromised
Supply Chain Risk Management
Executive Orders
- EO 13636 Improving Critical Infrastructure Cybersecurity
- EO 13806 Assessing and Strengthening the Manufacturing and Defense Industrial Base and Supply Chain Resiliency of the United States
- Executive Order 13806 Report
- EO 13873 Securing the Information and Communications Technology and Services Supply Chain
- EO 13913 Establishing the Committee for the Assessment of Foreign Participation in the United States Telecommunications Services Sector
- EO 13984 Taking Additional Steps to Address the National Emergency with Respect to Significant Malicious Cyber-Enabled Activities
- EO 14005 Ensuring the Future Is Made in All of America by All of America's Workers
- EO 14017 America's Supply Chains
- EO 14024 Blocking Property with Respect to Specified Foreign Activities of the Government of the Russian Federation
- EO 14028 Improving the Nation's Cybersecurity
- EO 14034 Protecting Americans' Sensitive Data from Foreign Adversaries
Authorities, Policies, and Standards
- SECURE Technology Act: Establishment of the Federal Acquisition Security Council
- NIST Special Publication: Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations (May 2022) (NIST SP 800-161r1 PDF)
- DNI ICD 731 Supply Chain Risk Management for the Intelligence Community (PDF)
- DNI ICS 731-01 Supply Chain Criticality Assessment 20151002 (PDF)
- DNI ICS 731-02 Supply Chain Threat Assessments 20160517 (PDF)
- DNI ICS 731-03 Supply Chain Information Sharing (PDF)
- DNI ICS 731-04 Supply Chain Vulnerability Assessments (PDF)
- DNI ICS 731-05 Supply Chain Risk Assessments (PDF)
Tools
Reducing Threats to Key U.S. Supply Chains
- NTIA Releases Minimum Elements for a Software Bill of Materials
- NCSC Supply Chain Risk Management Tri-Fold: Reducing Threats to Key U.S. Supply Chains (PDF)
Podcasts
- Authorized Disclosures Podcast: Cyber and Supply Chain Security Discussion with ONCD
- Podcast: Supply Chain Security Discussion with CBP
- Podcast on How One Federal Program Worked to Enhance its Supply Chain Security
- Podcast on Cyber & Supply Chain Threats to the Health Care Sector
- Podcast: Securing U.S. Supply Chains - Addressing Our Vulnerabilities with Jeanette McMillian





